TryhackMe - Phishing Studies

Ive done this exercise in the THM and then I came back 3 days later to do it again and take some notes so I can document the process when I need to investigate a similar email in the future.
*This is not intended to be a way to give the answer or expose the content of the site.
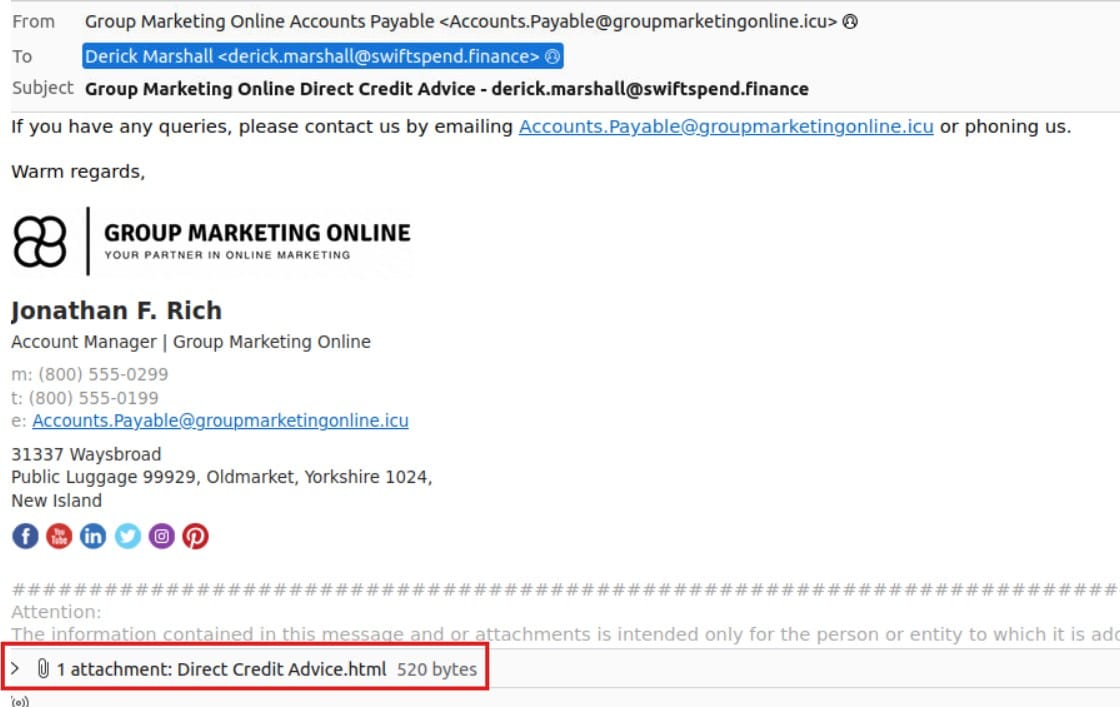
Email Example with the HTML attachment.
Ive opened the email Header and found the line where it deals with the attachment. As you can see its encoded using base64.
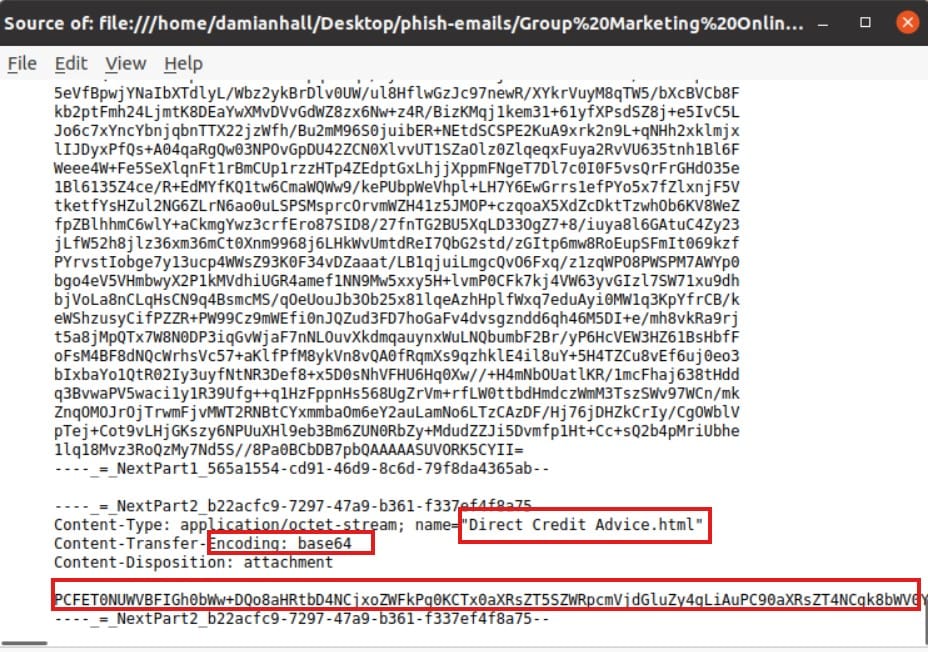
Encoded : PCFET0NUWVBFIGh0bWw+DQo8aHRtbD4NCjxoZWFkPg0KCTx0aXRsZT5SZWRpcmVjdGluZy4gLiAuPC90aXRsZT4NCgk8bWV0YSBodHRwLWVxdWl2PSJyZWZyZXNoIiBjb250ZW50PSIwO1VSTD0naHR0cDovL2tlbm5hcm9hZHMuYnV6ei9kYXRhL1VwZGF0ZTM2NS9vZmZpY2UzNjUvNDBlN2JhYTJmODI2YTU3ZmNmMDRlNTIwMjUyNmY4YmQvP2VtYWlsPWRlcmljay5tYXJzaGFsbEBzd2lmdHNwZW5kLmZpbmFuY2UmZXJyb3InIiAvPg0KPC9oZWFkPg0KPGJvZHk+DQoJPGgxPlJlZGlyZWN0aW5nLiAuIC48L2gxPg0KCTxwPklmIHlvdSBhcmUgbm90IHJlZGlyZWN0ZWQgYXV0b21hdGljYWxseSwgcGxlYXNlIGNsaWNrIDxhIGhyZWY9Imh0dHA6Ly9rZW5uYXJvYWRzLmJ1enovZGF0YS9VcGRhdGUzNjUvb2ZmaWNlMzY1LzQwZTdiYWEyZjgyNmE1N2ZjZjA0ZTUyMDI1MjZmOGJkLz9lbWFpbD1kZXJpY2subWFyc2hhbGxAc3dpZnRzcGVuZC5maW5hbmNlJmVycm9yIj5oZXJlPC9hPi48L3A+DQo8L2JvZHk+DQo8L2h0bWw+DQ==
Used Cyberchef.org to decode.
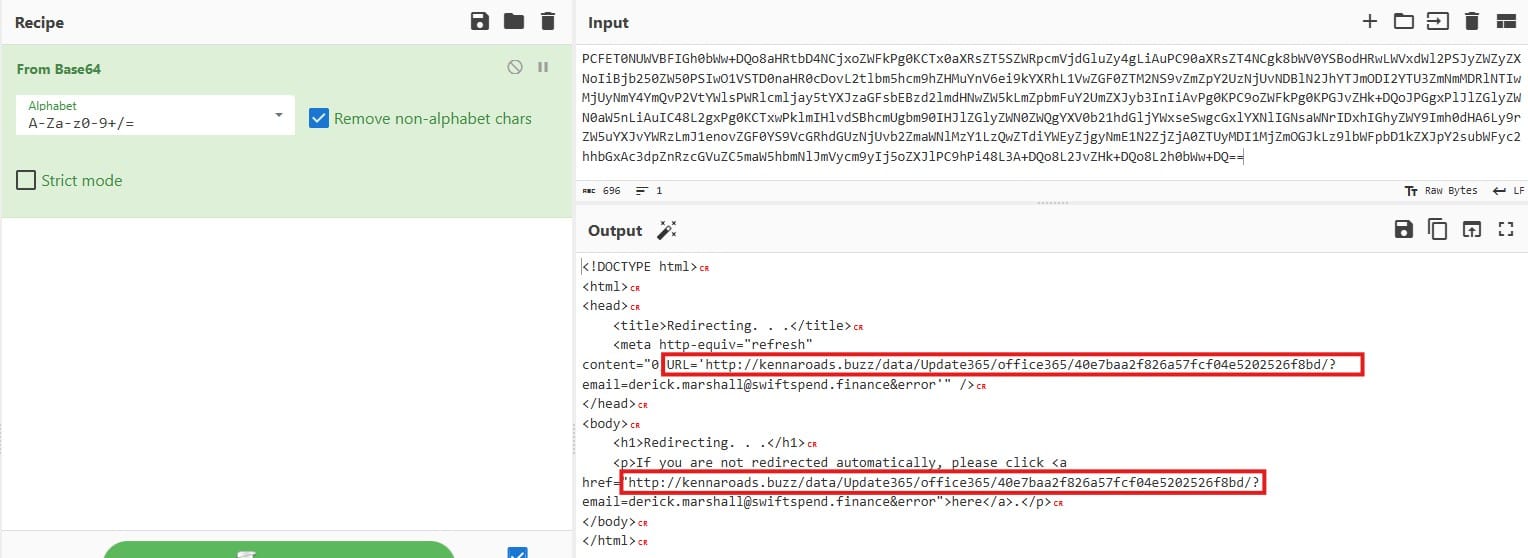
Found the URL.
To avoid clicking accidentally, we need to Defang it.
hxxp[://]kennaroads[.]buzz/data/Update365/office365/40e7baa2f826a57fcf04e5202526f8bd/?
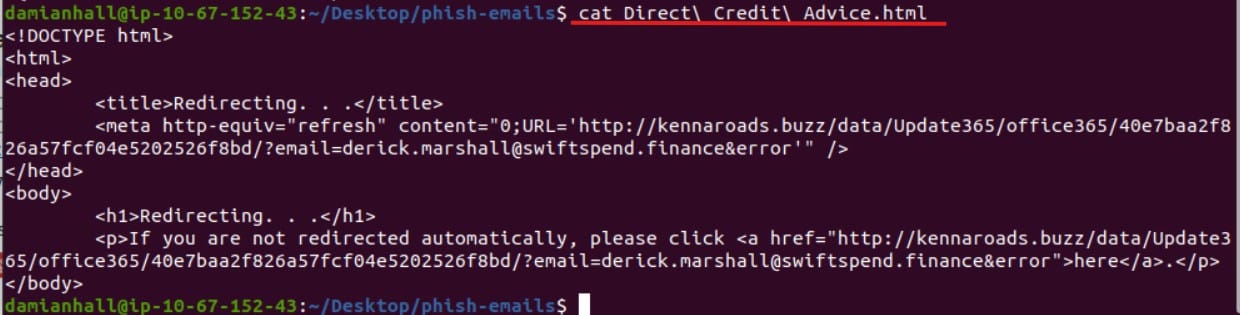
If we had saved the attachment we could also extract the information by using the command "cat".
If we navigate to : hxxp[://]kennaroads[.]buzz/data we can see some files.
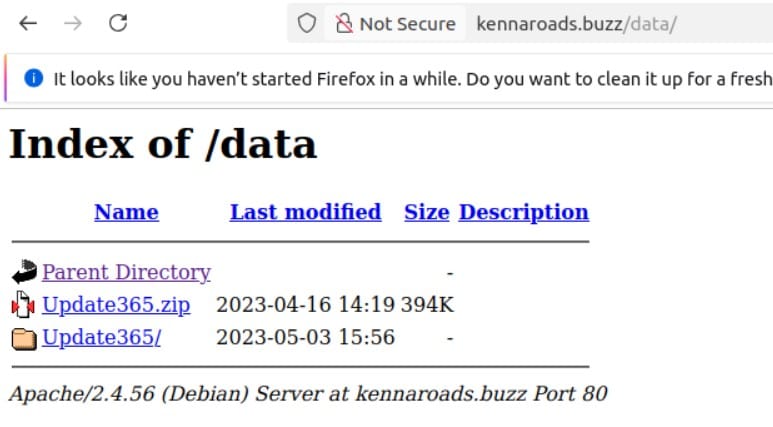
The wordpress website host a zip file, most likely containing the phishing kit. Download it. ** Ive downloaded using the THM environment (VM). **
When we extracted the zip we can see the files used for the phishing.
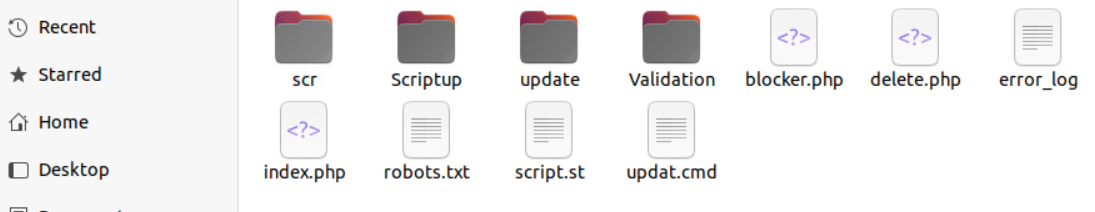
Im not going in detail about whats in each folder. My goal was to be able to find the files again and document the steps ive taken.