If Your DC Can Print, You Have a Problem
Why am I writing about this? The print nightmare happened in 2021.
Well, I was asked to disable the spooler on the Domain Controllers, so Why not create a post about it?
Background info :
"On Tuesday July 6, 2021, Microsoft issued CVE-2021-34527 regarding a Windows Print Spooler vulnerability. Updates were released on July 6 and 7 which addressed the vulnerability for all supported Windows versions. We encourage customers to update as soon as possible." Microsoft
" A remote code execution vulnerability exists when the Windows Print Spooler service improperly performs privileged file operations. An attacker who successfully exploited this vulnerability could run arbitrary code with SYSTEM privileges. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights." Microsoft
Why does Print Spooler matter here?
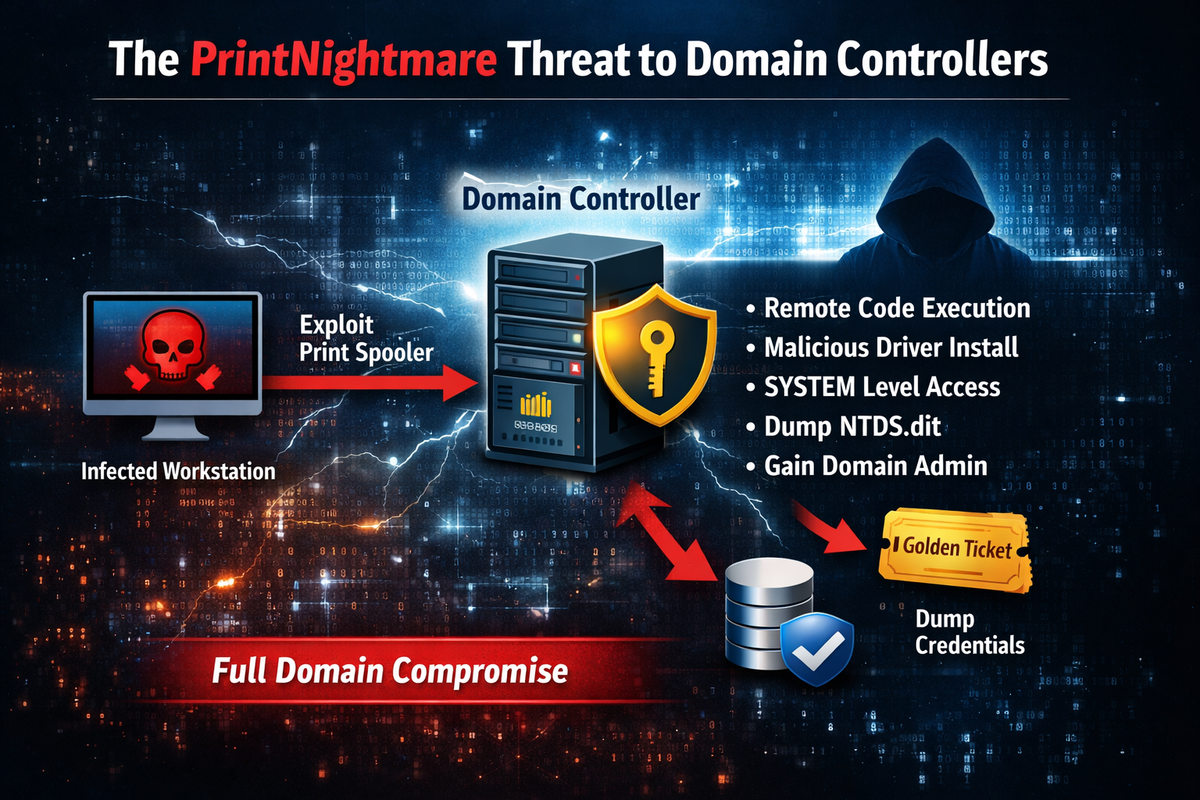
Because vulnerabilities like PrintNightmare were (and the spooler attack surface still can be) a path to:
- Remote code execution / privilege escalation on the DC, often ending up as LOCAL SYSTEM
- With SYSTEM (or equivalent high privilege), the attacker can access the capabilities needed to extract AD secrets — including copying from VSS snapshots or abusing backup-style APIs/rights.
The danger is: spooler gives you a foothold on a Tier-0 system, and once you’re SYSTEM on a DC, NTDS.dit extraction becomes a very realistic next step. NTDS.dit is the Active Directory database file on a Domain Controller, it contains Password hashes, account metadata. Once hashes can be extracted , it can be used to crack weak passwords and potentially compromise domain admin / enterprise admin accounts.
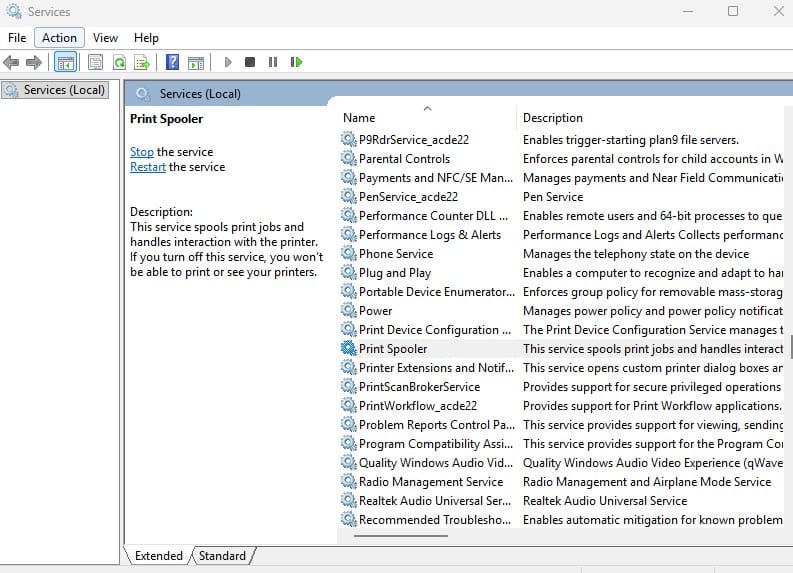
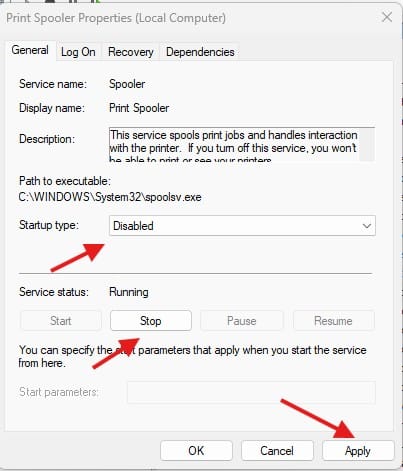
You can disable the spooler service by GPO, script and manually from the Services window.
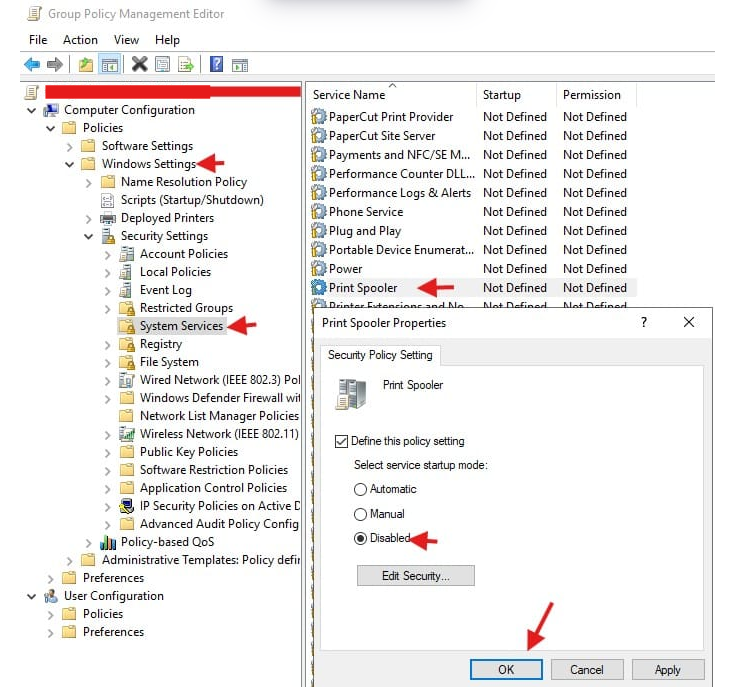
Using Group Policy: Computer Configuration >Policies>Windows Settings > Security Settings > System Services > Print Spooler > Disable > OK
Manually
The funny part about of this. I couldnt do anything, because this was my print server. OOOPss.